Introduction to Networks v7.0 – ITNv7 Practice Final Exam Answers
- SSH
- TFTP
- DHCP
- DNS

- the amount of data that can be sent at one time
- the amount of data that can be sent before an acknowledgment is required
- the total number of bits received during this TCP session
- a random number that is used in establishing a connection with the 3-way handshake
- well-known
- private or dynamic
- public
- registered
Registered Ports: 1024 through 49151.
Dynamic/Private : 49152 through 65535.

- The entire command, configure terminal, must be used.
- The administrator is already in global configuration mode.
- The administrator must first enter privileged EXEC mode before issuing the command.
- The administrator must connect via the console port to access global configuration mode.
- if the TCP/IP stack is functioning on the PC without putting traffic on the wire
- if there is connectivity with the destination device
- the path that traffic will take to reach the destination
- what type of device is at the destination
- An SVI is created in software and requires a configured IP address and a subnet mask in order to provide remote access to the switch.
- Although it is a virtual interface, it needs to have physical hardware on the device associated with it.
- SVIs do not require the no shutdown command to become enabled.
- SVIs come preconfigured on Cisco switches.

- The switch notifies the source of the bad frame.
- The switch places the new CRC value in the FCS field and forwards the frame.
- The switch drops the frame.
- The switch floods the frame to all ports except the port through which the frame arrived to notify the hosts of the error.
- The fragment-free switching offers the lowest level of latency.
- Fast-forward switching can be viewed as a compromise between store-and-forward switching and fragment-free switching.
- Fragment-free switching is the typical cut-through method of switching.
- Packets can be relayed with errors when fast-forward switching is used.
- using the incorrect cable type
- half-duplex operations
- a malfunctioning NIC
- electrical interference on serial interfaces
- CRC errors
- places information in the Ethernet frame that identifies which network layer protocol is being encapsulated by the frame
- adds Ethernet control information to network protocol data
- implements CSMA/CD over legacy shared half-duplex media
- applies source and destination MAC addresses to Ethernet frame
- integrates Layer 2 flows between 10 Gigabit Ethernet over fiber and 1 Gigabit Ethernet over copper
- nslookup cisco.com
- ping cisco.com
- ipconfig /flushdns
- net cisco.com
- nbtstat cisco.com
- Add a second NIC to the web server.
- Add a connection to the Internet via a DSL line to another ISP.
- Add another web server to prepare failover support.
- Add multiple connections between the switches and the edge router.
- copy running-config startup-config
- show interfaces
- show ip nat translations
- show running-config
Floor(config)# interface gi0/1
Floor(config-if)# description Connects to the Registrar LAN
Floor(config-if)# ip address 192.168.235.234 255.255.255.0
Floor(config-if)# no shutdown
Floor(config-if)# interface gi0/0
Floor(config-if)# description Connects to the Manager LAN
Floor(config-if)# ip address 192.168.234.114 255.255.255.0
Floor(config-if)# no shutdown
Floor(config-if)# interface s0/0/0
Floor(config-if)# description Connects to the ISP
Floor(config-if)# ip address 10.234.235.254 255.255.255.0
Floor(config-if)# no shutdown
Floor(config-if)# interface s0/0/1
Floor(config-if)# description Connects to the Head Office WAN
Floor(config-if)# ip address 203.0.113.3 255.255.255.0
Floor(config-if)# no shutdown
Floor(config-if)# end
- 192.168.235.234
- 203.0.113.3
- 192.168.235.1
- 10.234.235.254
- 192.168.234.114


- The IOS image is corrupt.
- Cisco IOS is missing from flash memory.
- The configuration file is missing from NVRAM.
- The POST process has detected hardware failure.
18. What service is provided by POP3?
- Retrieves email from the server by downloading the email to the local mail application of the client.
- An application that allows real-time chatting among remote users.
- Allows remote access to network devices and servers.
- Uses encryption to provide secure remote access to network devices and servers.
- peer-to-peer
- client-based
- master-slave
- point-to-point
20. Which command is used to manually query a DNS server to resolve a specific host name?
- tracert
- ipconfig /displaydns
- nslookup
- net
- bits
- frame
- packet
- segment
22. Which two OSI model layers have the same functionality as two layers of the TCP/IP model? (Choose two.)
- data link
- network
- physical
- session
- transport
23. Which three layers of the OSI model are comparable in function to the application layer of the TCP/IP model? (Choose three.)
- presentation
- physical
- network
- data link
- transport
- application
- session
* local router WAN interface: 198.133.219.33 / 2001:db8:FACE:39::10
* remote server: 192.135.250.103
- verifying that there is connectivity within the local network
- creating a network performance benchmark to a server on the company intranet
- determining the path to reach the remote server
- verifying that there is connectivity to the internet
- neighbor solicitation
- router advertisement
- router solicitation
- protocol unreachable
- route redirection
- pinging a host computer that has the IP address 127.0.0.1 on the network
- tracing the path to a host computer on the network and the network has the IP address 127.0.0.1
- checking the IP address on the network card
- testing the integrity of the TCP/IP stack on the local machine
- the virtually unlimited availability of IPv6 addresses
- the use of CSMA/CA
- the use of full-duplex capable Layer 2 switches
- the development of half-duplex switch operation
- the use of Gigabit Ethernet speeds
28. What does a router do when it receives a Layer 2 frame over the network medium?
- re-encapsulates the packet into a new frame
- forwards the new frame appropriate to the medium of that segment of the physical network
- determines the best path
- de-encapsulates the frame
- SFD
- LLC
- CSMA
- MAC
- FCS
- bus
- extended star
- ring
- partial mesh
31. Given network 172.18.109.0, which subnet mask would be used if 6 host bits were available?
- 255.255.192.0
- 255.255.224.0
- 255.255.255.192
- 255.255.255.248
- 255.255.255.252

- link-local
- public
- loopback
- multicast
- subnetwork address
- unicast address
- multicast address
- broadcast address
- Because IPv6 has integrated security, there is no need to hide the IPv6 addresses of internal networks.
- The problems that are induced by NAT applications are solved because the IPv6 header improves packet handling by intermediate routers.
- The end-to-end connectivity problems that are caused by NAT are solved because the number of routes increases with the number of nodes that are connected to the Internet.
- Any host or user can get a public IPv6 network address because the number of available IPv6 addresses is extremely large.
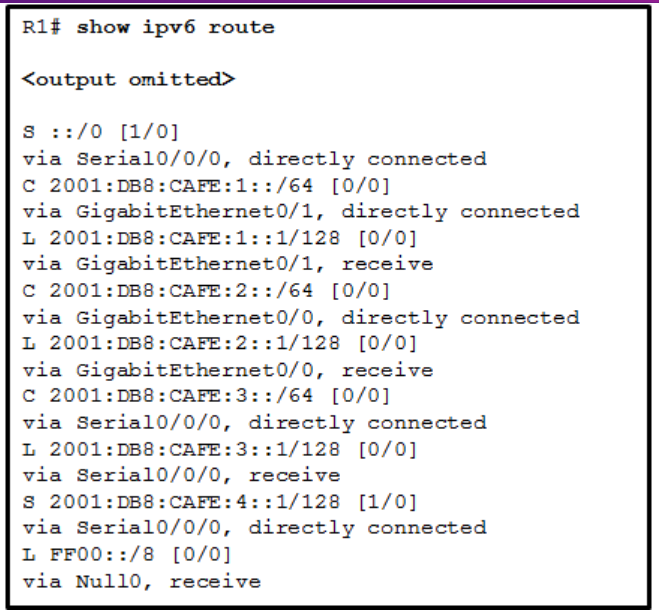
- directly-connected routes
- local routes
- remote routes
- C and L source routes
37. Which term describes a field in the IPv4 packet header that contains a unicast, multicast, or broadcast address?
- destination IPv4 address
- protocol
- TTL
- header checksum
- There is no impact on communications.
- The host is unable to communicate on the local network.
- The host can communicate with other hosts on the local network, but is unable to communicate with hosts on remote networks.
- The host can communicate with other hosts on remote networks, but is unable to communicate with hosts on the local network.
- fe80:9ea:0:2200::fe0:290
- fe80:9ea0::2020::bf:e0:9290
- fe80::220:b3f:f0e0:29
- fe80:9ea0::2020:0:bf:e0:9290

- ::1/128
- fe80::30d0:115:3f57:fe4c/128
- fe80::/64
- 2001:0:9d38:6ab8:30d0:115:3f57:fe4c/128
41. What type of IPv6 address is represented by ::1/128?
- EUI-64 generated link-local
- global unicast
- unspecified
- loopback
- It supports growth over time in accordance with approved network design procedures.
- It synchronizes traffic flows using timestamps.
- It ensures sensitive corporate data is available for authorized users.
- It prioritizes data flows in order to give priority to delay-sensitive traffic.
- wireless LAN controller
- server
- assembly line robots
- IPS
- gaming console
- retail scanner
- software that is installed on a user device and collects information about the user
- the use of stolen credentials to access private data
- an attack that slows or crashes a device or network service
- a network device that filters access and traffic coming into a network

- The switch will discard the frame.
- The switch will forward the frame to all ports.
- The switch will forward the frame only to port 2.
- The switch will forward the frame only to ports 1 and 3.
- The switch will forward the frame to all ports except port 4.
- 0.0.0.0
- 255.255.255.255
- the physical address of the destination host
- FFFF.FFFF.FFFF
- AAAA.AAAA.AAAA

- SW1 will send an ARP reply with its Fa0/1 MAC address.
- RT1 will send an ARP reply with its own Fa0/0 MAC address.
- RT1 will forward the ARP request to PC3.
- RT1 will send an ARP reply with the PC3 MAC address.
- RT1 will send an ARP reply with its own Fa0/1 MAC address.
- a user who is trying to guess a password to access the router
- a worm that is attempting to access another part of the network
- an unidentified individual who is trying to access the network equipment room
- a device that is trying to inspect the traffic on a link
49. Which statement describes the characteristics of packet-filtering and stateful firewalls as they relate to the OSI model?
- A packet-filtering firewall uses session layer information to track the state of a connection, whereas a stateful firewall uses application layer information to track the state of a connection.
- Both stateful and packet-filtering firewalls can filter at the application layer.
- A packet-filtering firewall typically can filter up to the transport layer, whereas a stateful firewall can filter up to the session layer.
- A stateful firewall can filter application layer information, whereas a packet-filtering firewall cannot filter beyond the network layer.
- Empty the browser cache.
- Use antivirus software.
- Delete unused software.
- Keep software up to date.
- Defragment the hard disk.
51. The employees and residents of Ciscoville cannot access the Internet or any remote web-based services. IT workers quickly determine that the city firewall is being flooded with so much traffic that a breakdown of connectivity to the Internet is occurring. Which type of attack is being launched at Ciscoville?
- access
- Trojan horse
- reconnaissance
- DoS
- Fiber-optic cabling does not conduct electricity.
- Multimode fiber-optic cabling carries signals from multiple sending devices.
- Fiber-optic cabling is primarily used as backbone cabling.
- Fiber-optic cabling uses LEDs for single-mode cables and laser technology for multimode cables.
- Fiber-optic cabling has high signal loss.
- latency
- goodput
- throughput
- bandwidth

- 10 Mb/s
- 1000 Mb/s
- 128 kb/s
- 100 Mb/s